Processes in research and teaching as well as in administration are increasingly dependent on the secure functioning of information and communication technology. At the same time, the number of potential threats is increasing by leaps and bounds. Bauhaus-Universität Weimar is taking this development into account by implementing the recommendations of the Federal Office for Information Security (BSI). The BSI is the federal government's cyber security authority.
Why BSI protection?
»The BSI's basic IT protection is a proven methodology for raising the level of information security in public authorities and companies of all sizes. The offerings of basic IT protection are considered the benchmark in administration and business when it comes to securing information and setting up an information security management system (ISMS). In this context, basic IT protection is also internationally respected due to its compatibility with ISO 27001.«
The recommendations of the BSI serve to protect against damage and are binding for all processes in which data with a high or very high protection requirement are processed. This also results in changes and restrictions to familiar programs and processes, which we would like to explain to you here.
Main implemented features
- A so-called TPM chip is installed in BSI-compliant, administered computers. A Trusted Platform Module (TPM) is a microchip on computers or in electronic devices. It provides basic security functions on a hardware basis and can generate cryptographic keys, store them securely or control their use.
- BitLocker encryption: BitLocker is a hard disk encryption that is used on the University's individual computers. BitLocker starts before the operating system and accesses the TPM chip by default.
- Add-in protection for Microsoft Office programs: Only defined add-ins can be used in Office products. Add-ins are ready-made functions or macros that can be included in programs and fully integrated into the main program.
- Encryption specifications for Microsoft Office programs were implemented according to the specifications of the BSI.
- Message format set in Outlook: E-mails are sent and received in plain text by default.
Changes to Microsoft Office programs
General
General settings can be viewed in the Office programs via »Options - Add-ins« or »Options - Trust Center«.
ActiveX controls disabled
The use of ActiveX controls is no longer possible.
An ActiveX control is a program object that can be reused by many computer applications or between computers in a network. It is often used in forms in Word or Excel when buttons, checkboxes, radio buttons, etc. are to be used. On BSI-compliant computers, only standard controls, not custom-developed elements, are allowed in documents. The standard controls have the same functionalities as ActiveX controls, but cannot be adapted as extensively optically. On the other hand, they can be used with Mac OS, so that the exchange of documents between Windows and Mac OS is improved.
Why was the use of ActiveX controls restricted?
ActiveX is not executed in isolation, but runs unsecured on the computer. For example, sensitive data could be read from your hard drive by visiting a suitably prepared website.
The developer tools are not displayed in Excel, Word and Outlook
The ribbon in the Office programs may not be customised, but you can activate the developer tools via entries in the registry data. Please contact the SCC user service for this.
Unsigned macros cannot be executed in Microsoft Office programs
A macro is a small piece of program code that enables recurring processes or certain functions to be carried out automatically. Macros are often used in Word or Excel documents. The settings according to the BSI requirements prevent macros that are not signed from being executed. Macros (also VBA: Visual Basic for Applications) that have been digitally signed can be executed.
There are two ways to sign macros:
- Office documents are signed centrally by SCC.
To do so, please contact the SCC User Service. - You sign the Office macro yourself.
You sign the Office macro yourself: Certify Office macros
A certificate must be available with which programs can be signed.typo3/#_msocom_1
- Open the macro file in Office
- Then open the Visual Basic Editor with »ALT+F11«
- Then select »Extras« à »Digital Signatures«
- Click on »Select« under »Signed as«
- Now select the certificate.
If the corresponding certificate is not displayed, select it via »More options« and finish with »OK«. - Save and close the Office document. Afterwards, the macros can be executed in the document.
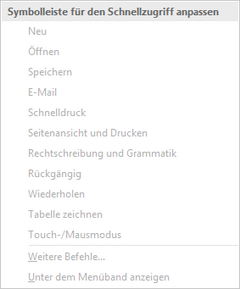
Quick launch menu bar and ribbon interface cannot be customised in Office programs
Creating forms in Word
To be able to create forms yourself, you must be included in a corresponding system administrator group for the special authorisations. Only then is it possible to create forms with Word.
To do so, please contact the SCC User Service by e-mail:
nutzerservice[at]uni-weimar.de
Changes to Microsoft Office programs in detail
Word
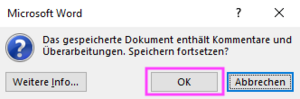
Warning when saving Word documents with comments
If you want to save a document with comments, the warning shown below appears:
»The saved document contains comments and revisions. Continue saving?«
The warning is a reminder that you may want to delete unwanted comments before publishing, printing, saving or sending the document.
Click on »OK« to save the document and keep the comments.
Excel
Unstable Excel window when moving with the mouse
If an Excel window is moved from full screen mode to individual screen mode and subsequently moved by mouse, e.g. from one screen to another in a multi-monitor workstation, then the moving of the window is very choppy. We were able to determine that this is due to the exploit protection for Excel. (An exploit represents a systematic way to break into computer systems due to vulnerabilities or security holes in the software). Working and also moving are possible, but is made a little more difficult.
Macros in Excel
For explanation see »Unsigned macros cannot be executed in Microsoft Office programs«
Please send the Excel file in question to our user service. This will then be signed by us and the macros can be used again from that point on.
Access
Table link manager does not show tables
If you want to link Access databases with each other or create references to another Access database, you can use the table link manager. However, the Link Manager only works if ActiveX controls can be executed in Office.
On request, we will provide you with an application that can be used to temporarily enable the ActiveX. Please note that the application is then not only available to you, but to all logged-in users on the respective computer. On request, we will provide you with an application that can be used to temporarily unlock the ActiveX. Please note that the application is then not only available to you, but to all logged-in users on the respective computer.
To do so, please contact our user service (e-mail: nutzerservice[at]uni-weimar.de; phone: +49 (0) 3643 / 58 24 24).
Data import as well as export to and from Access databases does not work
For import to or export from Access databases ActiveX controls must be allowed for a short time. The procedure is identical as described in item »Table link manager does not display tables«.
Editing Access databases only on project drives
For Access databases to work without problems, they should be stored on a project drive. (Trusted location)
If you want to show and use an Access database during a presentation and you do not have access to the project drives, back up this database locally on your laptop.
Notice: Connecting to the project drive via »WebDrive« is not an optimal solution, because this connection does not use the full namespace (network path) of the project drive, but a local drive letter. This means that the share for the database is not effective.
E-mails and Outlook
Receive and send mail in »plain text« format
Many e-mails today are sent in HTML format (colored, different fonts, embedded graphics). Malicious code can be hidden in the source code of an HTML-formatted e-mail, which is already executed on the recipient's computer when the e-mail is opened, without having to click on an attachment. Therefore, the SCC has implemented the BSI's recommendation and configured Outlook to send and receive emails in plain text format by default.
For individual e-mails, you can change these default settings as follows.
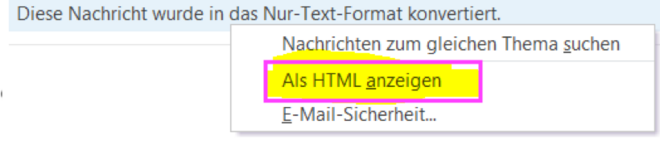
Show received mails in HTML
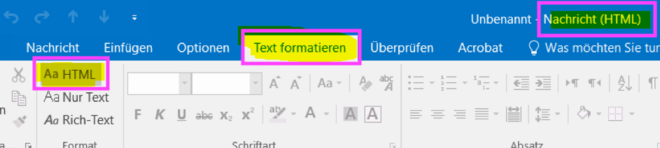
Incoming e-mails receive the following notice. (both in the preview and when displayed in the separate window):
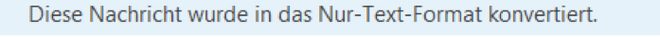
Sending mails in HTML
If you want to send an HTML e-mail, you can use the key combination »[ALT]-x-ö« (inside the e-mail in Outlook) to change the formatting from plain text to HTML.
Notice: Whether your message is displayed in HTML_ or plain text format depends on the individual settings in the receiving person's mail program.
Alternatively, use the menu on the »Format Text« tab within the e-mail:
Links in received mails are not displayed clickable as URL link
With the conversion of the display of e-mails to text-only format, links to e-mail and Internet addresses (URLs) are also no longer clickable. To access a link, you must copy and paste it into the address bar of your browser. Alternatively, switch the view to HTML as described above.
Exception: In self-composed mails, a URL is linked in the usual way, i.e. with a blue background and clickable.
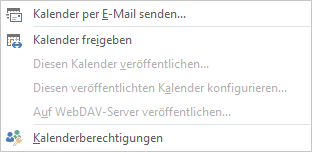
Publish calendar on the Internet not possible
You can only publish a calendar within your own Exchange structure, i.e. with members of Bauhaus-Universität Weimar. Publishing on other platforms, like a WebDAV server etc., is inactive.
You can still share or even send your calendar via Outlook as well as OWA.
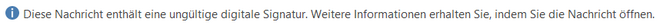
Mails with expired certificates are no longer displayed in Outlook
A digital signature lets you sign documents digitally. A digital signature is an authentication tool that confirms that messages come from a known source and have not been altered during transmission. When a digital signature is properly implemented, the receiving person can assume that the message was sent by the specified sender(s).
If you receive an e-mail with an invalid signature, this message will not be displayed at first, but you will see an empty preview window with the following warning:
If you still want to read the email, double-click the corresponding message (in the list) and another message will be displayed:

Blocking mail attachments with potentially dangerous content
Potentially dangerous attachments from external senders are no longer delivered via email. You, as the recipient, will receive the original email, but the system will automatically delete the »suspicious« attachments and attach a txt file informing you of the reason for the deletion.
Potentially dangerous attachments include older Microsoft Office formats (MS Office 2003 or older). With these file types, it is not directly recognizable whether they may contain harmful macros. More information and a list of blocked file formats can be found on the SCC pages under »Blocking e-mail attachments«.
If, in exceptional cases, you need to exchange such files with known, trusted partners*, we recommend using the university cloud at cloud.uni-weimar.de
Changes in Adobe Acrobat products
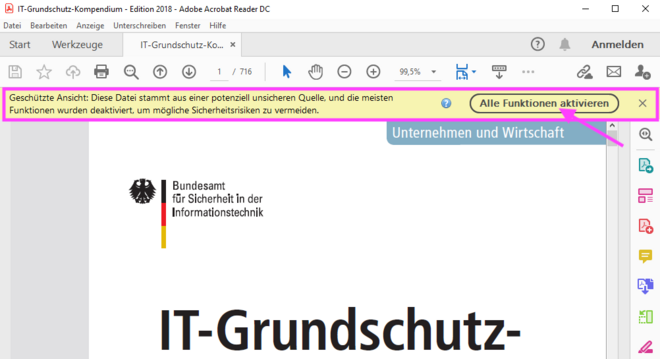
PDF documents are opened in protected mode
Clicking »Enable all functions« will disable the protected mode for the currently opened document. Disabling is not necessary for just reading the files. This setting is intended to sensitize you not to carelessly trust PDF documents from unknown sources and open them without thinking. If you are sure that the PDF file is from a trusted source, you can disable protected mode at any time.
Adobe Acrobat DC: When you need to edit PDFs
Currently, »Acrobat Reader DC« is deployed on all Windows devices and is the default program for opening PDF files.
If you want to edit PDF documents, you have to open the file actively with »Adobe Acrobat DC« (not via double click, this calls Acrobat Reader). To do this, please follow the steps described on the following page:
»Adobe Named User Licenses (NUL) for employees«
This software may need to be installed on your device.